



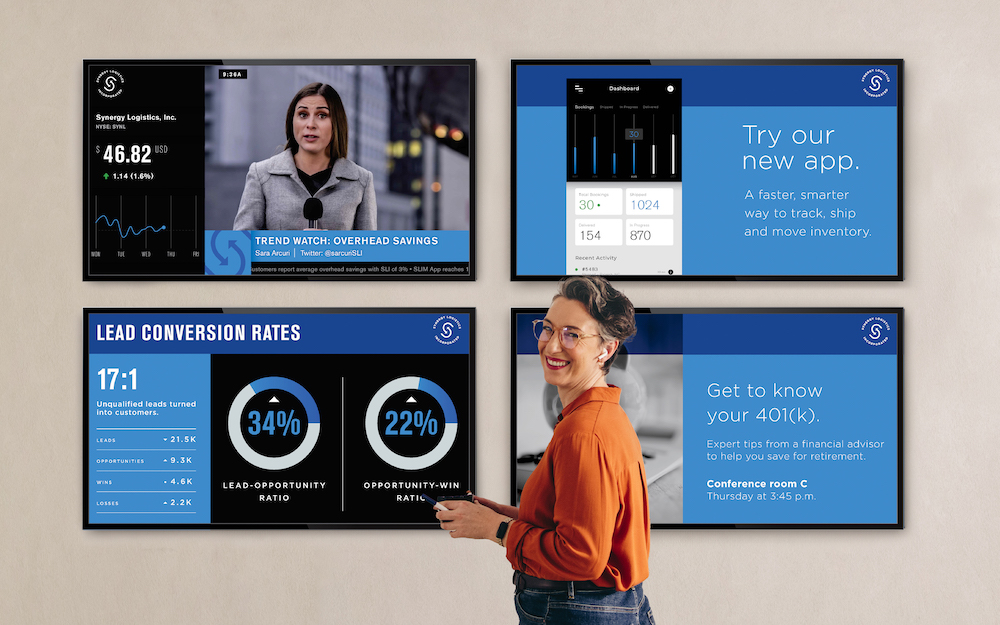
Skykit Beam redefines digital signage, offering a seamless and captivating way to communicate your message to any audience. Easily manage content, engage your audience, and maintain a dynamic brand across networks of any scale. Whether you’re a small business owner or a communications manager at a large corporation, Skykit Beam puts the power of engaging digital signage at your fingertips.
Skykit has all of the features we need in one application. It’s one of the most intuitive and simple-to-navigate digital signage platforms we have ever used. The user interface is so simple!
Head of Retail Sales
We’re using Skykit to get information out to our students and staff efficiently. Now, we have big visuals for everyone to see as they enter the building. Not many schools have big display walls like we do!
Education Coordinator
We are seeing huge cost-savings after switching to Skykit when you consider maintenance, software updates, and tech support for each location. We spend less time chasing down problems now.
Director of IT

Use the apps and tools you love to create and display amazing digital signage content.
Whether you prefer Adobe Photoshop, Adobe Illustrator, Canva, or any other design tool, Skykit Beam lets you integrate them easily and show off your creativity on your screens.
Share real-time performance metrics securely on any screen!
Display Power BI, Tableau, Salesforce, Domo, and countless other live dashboards to inspire teams and enable them to make informed decisions at a glance.
Skykit Control is your ultimate solution for efficient Android device management specifically tailored for digital displays and kiosks. Control is designed to streamline IT support, reduce operational costs, and maximize device uptime.
